Advanced Cybersecurity
- Level High School
- Contact Hours 145
- Timeframe Year
In this course, students build on their foundational cybersecurity knowledge to explore complex concepts in data protection, secure communications, and threat defense. Through interactive lessons, hands-on coding, and investigative projects, students uncover how data is protected, communications verified, and cyber threats mitigated. They’ll take on the roles of cryptographers, forensic analysts, and network architects as they tackle real-world security challenges and engineer creative solutions. With projects like building steganographic tools and crafting security policies, students gain both technical expertise and critical thinking skills for the digital age.
To view the entire syllabus, click here or click to explore the full course.
|
Advanced Cryptography
In this module, students will deepen their understanding of modern cryptographic systems by exploring advanced concepts like public key encryption, hashing, digital certificates, and password salting. Through lessons, articles, code exercises, and creative assignments, they’ll learn how encryption secures data, how hashing algorithms are constructed and attacked, and how secure communications are verified and maintained online. |
|
Project: Steganography
In this project, students will explore how steganography allows messages to be hidden in plain sight, often within images, text, or other media. Students will learn real-world applications of this practice, analyze encryption methods, and create their own image-based steganography projects. The module culminates in peer-to-peer decoding and reflection activities. |
|
Cyber Defense
In this module, students will investigate the various forms of cyberattacks and the methods used to carry them out. They will distinguish between threats, vulnerabilities, and exploits, analyze different types of malware and network attacks, and explore real-world prevention strategies. |
|
Threats & Security Principles
In this module, students will explore foundational security concepts and apply them through real-world scenarios and simulations. They will learn to distinguish between threats, vulnerabilities, and exploits; investigate actual data breaches; evaluate ethical concerns; and examine how protocols and baseline security measures defend against attacks. |
|
Project: Digital Forensics
In this project, students will step into the role of digital forensic investigators, using real-world techniques to analyze system logs, metadata, and image data. Through hands-on scenarios, they will learn how digital footprints can be uncovered and interpreted to solve cyber incidents, identify misuse, and verify or disprove claims in both criminal and non-criminal investigations. |
|
Advanced Networking
In this module, students explore and research network infrastructures and network security. They will demonstrate how to set up a virtual private network (VPN), and design and configure different types of networks. Students will also take a look at firewalls and how to initiate port scans. |
|
Networking Infrastructure
In this module, students explore the foundational elements that make up digital communication systems, guiding students through the history, components, and security of computer networks. Students analyze network models, services, and tools, and simulate both theoretical and practical aspects of network design and security. |
|
Project: The Inside Scoop on LANs
In this project, students will create a "magazine" that explains key concepts about Local Area Networks (LANs), topologies, Ethernet standards, and LAN cabling. Students will research and present the information in a magazine-style layout with sections, images, and creative design. |
|
Risk Management
In this module, students demonstrate skills in conducting vulnerability scans and recognizing vulnerabilities in security systems. They will conduct a security audit and examine port scanning, packet sniffing, and proxy servers to discover exploits in a system. Students also are able to recommend security measures to mitigate the vulnerabilities. |
|
Project: Put it in Writing!
In this project, students develop a training policy that informs employees on matters of network security and details the company policy on preventative measures employees should take. |
|
Databases
In this module, students will explore the fundamentals of SQL and relational databases, including structuring data into tables and writing basic SELECT queries with filters. They will then deepen their skills by practicing advanced filtering, sorting, and data presentation using logical operators, compound conditions, and clauses like ORDER BY and AS. Finally, students will learn how to join multiple tables to solve complex data problems and simulate real-world database scenarios. |
|
Programming in Python
In this module, students are introduced to the fundamentals of programming by learning how to write basic code in Python using print statements, variables, user input, and arithmetic expressions. They’ll explore data types, string operations, comments, and the role of programming languages in creating interactive programs. |
|
Decisions in Programming
In this module, students expand their programming skills by working with Boolean values, logical and comparison operators, and if statements to create decision-making programs. They apply their understanding to secure coding practices and explore how programming decisions align with real-world cybersecurity policies and principles. |
|
Project: Engineering Design Process
In this project, students will learn the theory and practice of the engineering design process. This project allows students to think creatively about the applications of the concepts covered in the course, and create something of personal value. |
|
Final Exam
Students are assessed on topics learned throughout the course. |
Explore programs that your students will build throughout this course!
Here are a few examples of teacher resources and materials to use in the Advanced Cybersecurity course

The CodeHS Cybersecurity course prepares students with crucial skills to be responsible citizens in a digital future and protect themselves from the growing threat of cyber attacks. With the CodeHS online Professional Development course, we'll train teachers at your school to teach an excellent Cybersecurity course. No programming experience is required. Teachers will gain the skills, pedagogical knowledge, resources, and confidence to lead a great cybersecurity class with CodeHS.
View Units CodeHS PD OptionsAdvanced Cybersecurity is aligned with the following standards
| Standards Framework | View Alignment |
|---|---|
| Indiana Advanced Cybersecurity | View (100%) |
| South Carolina Advanced Cybersecurity | View (76%) |
| Colorado Cybersecurity II | View (60.6%) |
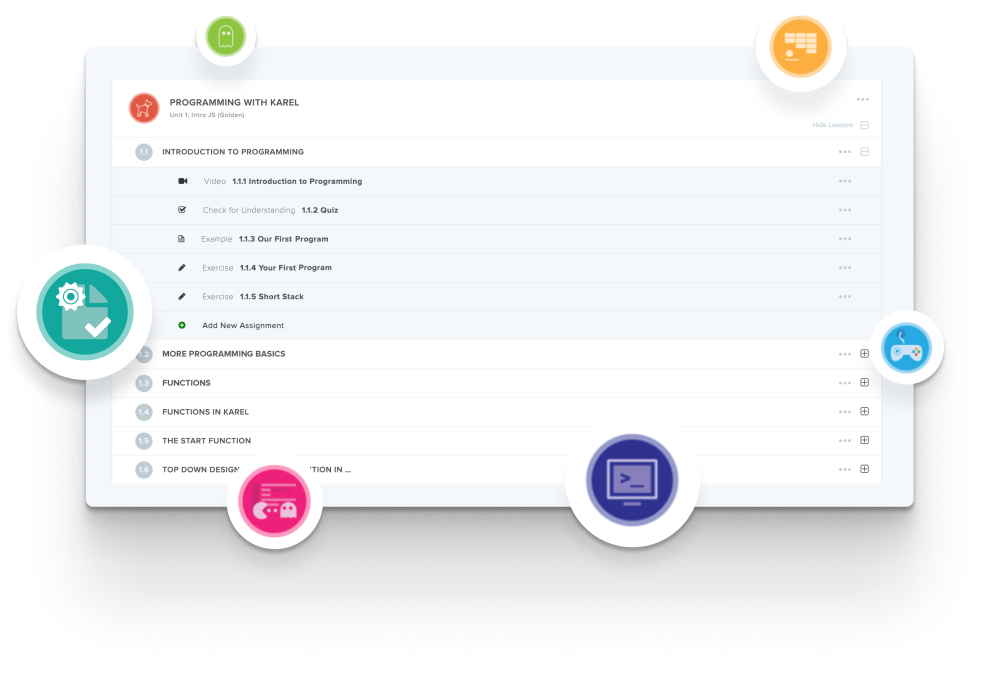
Create and organize Assignments in any CodeHS course that you're teaching. You can even add custom assignments to pre-existing CodeHS courses.
Learn MoreDidn't find what you were looking for? Here are a few links that might be useful to you.