Fundamentals of Cybersecurity (2020)
- Level High School
- Contact Hours 145
- Timeframe Year
This course is outdated and has been replaced by https://codehs.com/course/cyber_fundamentals/overview This is the first course in the cybersecurity pathway and will prepare students for an advanced cybersecurity course and/or cybersecurity certification(s). Students will learn cybersecurity topics such as software security, networking, system administration, and the basics of cryptography and programming.
To view the entire syllabus, click here or click to explore the full course.
|
What is Cybersecurity?
Students explore the basics of cybersecurity. Students learn about why cybersecurity is important, recent threats to cybersecurity, and different careers in the field. |
|
Digital Citizenship and Cyber Hygiene
Students learn about Internet etiquette and how to stay safe on the world wide web. Students also look at the potential effects of our digital footprints, how to protect information from online risks, and the implications of cyberbullying. |
|
Project: Public Service Announcement
For this project, students create a Public Service Announcement (PSA) to teach their peers about digital citizenship and cyber hygiene. |
|
Programming Fundamentals
Students learn the fundamentals of programming including variables, arrays, and objects as well as the difference in interpreted and compiled languages. Students explore programming through block coding which includes conditional statements and control structures. |
|
The ABCs of Cryptography
Students dive into the history of cryptography systems, the motivation behind using encryption systems, and basic cryptography systems. Additionally, students explore topics on how to use cryptography, cryptology, and cryptanalysis. |
|
Project: Classic Cipher Newscast
In this project, students write, rehearse, and perform a newscast with their team. Each team is given a different **classic cipher** (beyond Caesar and Vigenere) to research and address in their newscast. |
|
System Administration
Students compare and contrast common operating systems (Windows, Linux, OS) and explain the importance of application security. Students investigate security options and implement user accounts to enforce authentication and authorization. Students also demonstrate how to work with basic and advanced command prompts. |
|
Software Security
Students learn what happens when running a web application and how to look inside web apps using developer tools, source code, and more. Students learn basic SQL and common attacks like SQLi, and by the end of the module, students will be able to recommend solutions for flawed security systems. |
|
Networking Fundamentals
Students explore the structure and design of the internet and networks, and how this design affects the reliability of network communication, the security of data, and personal privacy. Students learn how the Internet connects computers all over the world by using networking protocols. |
|
IT Infrastructure
Students learn about the physical elements of computers and networking, such as motherboards, RAM, routers, and the use of port numbers, ethernet, and wireless devices. |
|
Project: Troubleshooting
In this project, students explore the troubleshooting methodology and utilize it to solve sample IT support issues. |
|
Final Exam
Students are assessed on topics learned throughout the course. |
|
What's Next?
Students explore the different pathways available to learn more about cybersecurity upon completing this course. |
Explore programs that your students will build throughout this course!
Here are a few examples of teacher resources and materials to use in the Fundamentals of Cybersecurity (2020) course
The CodeHS Cybersecurity Level 1 Certification offers high school students the opportunity to validate their mastery of Cybersecurity, giving them a competitive advantage when entering college or the workforce.
Learn More

The CodeHS Cybersecurity course prepares students with crucial skills to be responsible citizens in a digital future and protect themselves from the growing threat of cyber attacks. With the CodeHS online Professional Development course, we'll train teachers at your school to teach an excellent Cybersecurity course. No programming experience is required. Teachers will gain the skills, pedagogical knowledge, resources, and confidence to lead a great cybersecurity class with CodeHS.
View Units CodeHS PD OptionsFundamentals of Cybersecurity (2020) is aligned with the following standards
| Standards Framework | View Alignment |
|---|---|
| Indiana Cybersecurity Fundamentals | View (92.3%) |
| South Dakota Cybersecurity | View (90.9%) |
| Connecticut 3A | View (90%) |
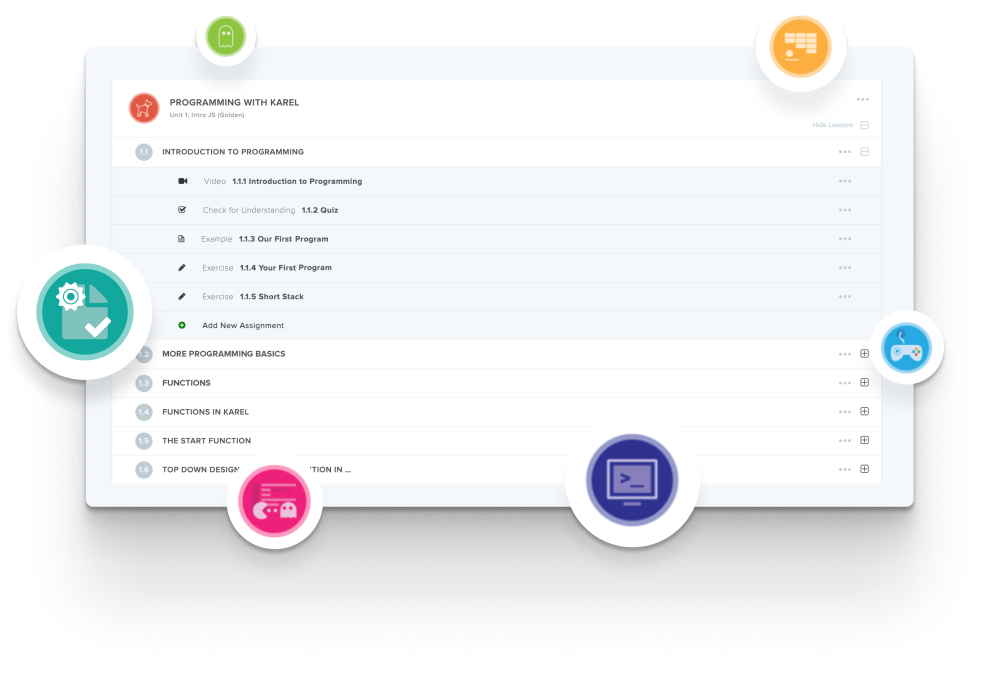
Create and organize Assignments in any CodeHS course that you're teaching. You can even add custom assignments to pre-existing CodeHS courses.
Learn MoreDidn't find what you were looking for? Here are a few links that might be useful to you.