South Carolina Cybersecurity Fundamentals
- Level High School
- Contact Hours 130
- Timeframe Year
This course examines the core concepts and terminology of cybersecurity and information assurance, integrating the importance of user involvement, network architecture, threats, and security; operational and system security; cryptography, and a broad range of other topics.
To view the entire syllabus, click here or click to explore the full course.
|
What is Cybersecurity?
Students explore the basics of cybersecurity. Students will learn about why cybersecurity is important, recent threats to cybersecurity, and different careers in the field. |
|
Digital Citizenship and Cyber Hygiene
Students learn digital etiquette in order to use the Internet safely, effectively, and ethically. |
|
Project: Public Service Announcement
Students create a Public Service Announcement (PSA) to teach their peers about digital citizenship and cyber hygiene. |
|
The ABCs of Cryptography
Students explore the history of cryptography systems, the motivation behind using encryption systems, and basic cryptography systems. |
|
Advanced Cryptography
Students apply advanced principles of cryptology, including Public Key Infrastructure and hash functions, encrypted email, digital certificates, and private key certificates. |
|
Project: Steganography
Students explore steganography and create your own encryption algorithm to conceal and hide a message within the pixels of an image. |
|
System Administration
Students investigate common operating systems, security options and implement user accounts to enforce authentication and authorization. |
|
Cyber Defense
Students learn basic SQL and common attacks like SQLi, and solutions for flawed security systems. |
|
Networking Fundamentals
Students explore the structure and design of the internet and networks, and how this design affects the reliability of network communication, the security of data, and personal privacy. |
|
IT Infrastructure
Students learn about the physical elements of computers and networking, such as motherboards, RAM, routers, and the use of port numbers, ethernet, and wireless devices. |
|
Project: Troubleshooting
Students explore the troubleshooting methodology and utilize it to solve sample IT support issues. |
|
Risk Management
Students conduct a security audit and examine port scanning, packet sniffing, and proxy servers to discover exploits in a system. |
|
Final Exam
Students demonstrate mastery of topics learned throughout the course. |
|
What's Next?
Students explore the different pathways available to learn more about cybersecurity upon completing this course. |
Explore programs that your students will build throughout this course!
Here are a few examples of teacher resources and materials to use in the South Carolina Cybersecurity Fundamentals course
The CodeHS Cybersecurity Level 1 Certification offers high school students the opportunity to validate their mastery of Cybersecurity, giving them a competitive advantage when entering college or the workforce.
Learn More
South Carolina Cybersecurity Fundamentals is aligned with the following standards
| Standards Framework | View Alignment |
|---|---|
| South Carolina Cybersecurity Fundamentals | View (95.1%) |
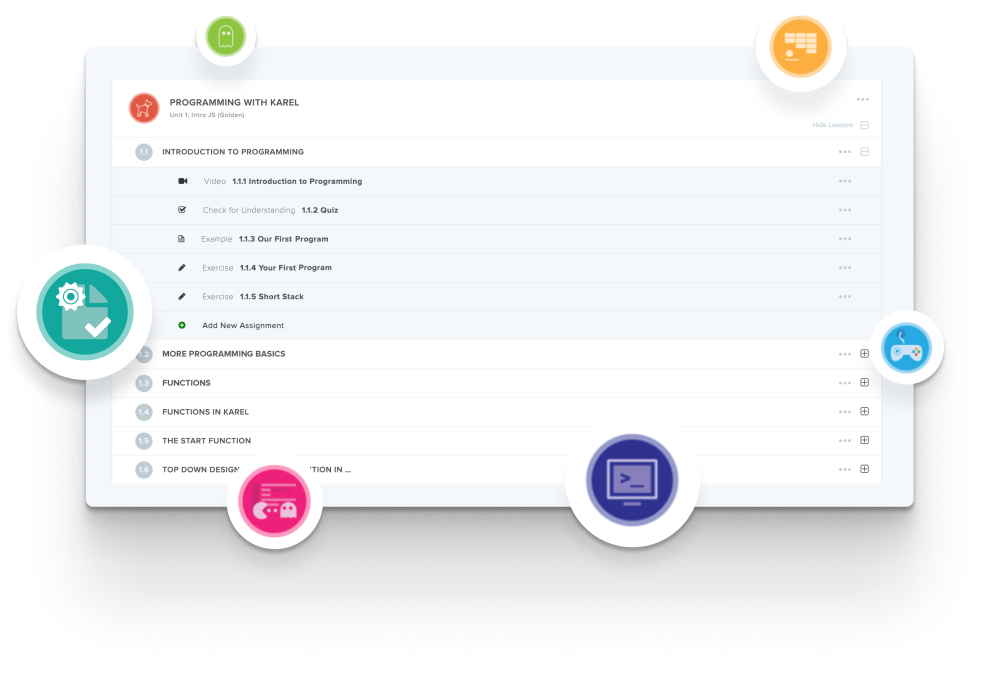
Create and organize Assignments in any CodeHS course that you're teaching. You can even add custom assignments to pre-existing CodeHS courses.
Learn MoreDidn't find what you were looking for? Here are a few links that might be useful to you.