Texas Foundations of Cybersecurity
- Level High School
- Contact Hours 155
- Timeframe Year
Students develop the knowledge and skills needed to explore fundamental concepts related to the ethics, laws, and operations of cybersecurity by examining trends and operations of cyberattacks, threats, and vulnerabilities. The skills obtained in this course prepare students for additional study in cybersecurity.
To view the entire syllabus, click here or click to explore the full course.
|
What is Cybersecurity?
Students explore the basics of cybersecurity. Students will learn about why cybersecurity is important, recent threats to cybersecurity, and different careers in the field. |
|
Digital Citizenship and Cyber Hygiene
Students learn topics on Internet etiquette, how to stay safe on the web, potential effects of digital footprints, how to protect their information, and the implications of cyberbullying. |
|
Project: Public Service Announcement
For this project, students create a Public Service Announcement (PSA) to teach their peers about digital citizenship and cyber hygiene. Students can select any of the topics covered so far. |
|
The ABCs of Cryptography
Students dive into the history of cryptography systems, the motivation behind using encryption systems, and basic cryptography systems. Additionally, students explore topics on how to use cryptography, cryptology, and cryptanalysis to decode a message without the use of a key. |
|
Project: Classic Cipher Newscast
In this project, students will get to create a newscast! This could be pre-recorded or presented live. Students will write, rehearse, and perform an approximately 5 – 10 minute newscast with their team. Each team will be given a different **classic cipher** (beyond Caesar and Vigenere) to research and address in their newscast. |
|
System Administration
Students compare and contrast common operating systems (Windows, Linux, OS) and explain the importance of application security. Students investigate security options and implement user accounts to enforce authentication and authorization. Students also demonstrate how to work with basic and advanced command prompts. |
|
Software Security
Students learn what happens when running a web application and how to look inside web apps using developer tools, source code, and more. Students learn basic SQL and common attacks like SQLi, and by the end of the module, students will be able to recommend solutions for flawed security systems. |
|
Networking Fundamentals
Students explore the structure and design of the internet and networks, and how this design affects the reliability of network communication, the security of data, and personal privacy. Students learn how the Internet connects computers all over the world by using networking protocols. |
|
IT Infrastructure
Students learn about the physical elements of computers and networking, such as motherboards, RAM, routers, and the use of port numbers, ethernet, and wireless devices. |
|
Project: Troubleshooting
In this project, students explore the troubleshooting methodology and utilize it to solve sample IT support issues. |
|
Project: IT Professional
In this project, you will explore cybersecurity career pathways and build skills that will be needed within these fields such as communication. |
|
Project: Digital Forensics
In this project, students will work through fictitious forensic cases to practice collecting, examining, analyzing and reporting on data that they have unveiled. |
|
Cyber Defense
In this module, you will explore different types of network attacks and how to build up security walls to defend against them. |
|
Project: Put it in Writing!
In this project, students develop a training policy that informs employees on matters of network security and details the company policy on preventative measures employees should take. |
|
Risk Management
In this module, you will demonstrate skills in conducting vulnerability scans and recognizing vulnerabilities in security systems. You will conduct a security audit and examine port scanning, packet sniffing, and proxy servers to discover exploits in a system. You will also be able to recommend security measures to mitigate the vulnerabilities. |
|
Project: The Game of Risk
In this project, you will design and create a board game or a card game that will help players to identify randomized security vulnerabilities and their appropriate defenses. |
Explore programs that your students will build throughout this course!
Here are a few examples of teacher resources and materials to use in the Texas Foundations of Cybersecurity course
The CodeHS Cybersecurity Level 1 Certification offers high school students the opportunity to validate their mastery of Cybersecurity, giving them a competitive advantage when entering college or the workforce.
Learn More
Texas Foundations of Cybersecurity is aligned with the following standards
| Standards Framework | View Alignment |
|---|---|
| Texas Foundations of Cybersecurity (NEW) | View (100%) |
| CompTIA Tech+ | View (100%) |
| Texas TEKS CTE Employability Skills (Levels 1-2) | View (100%) |
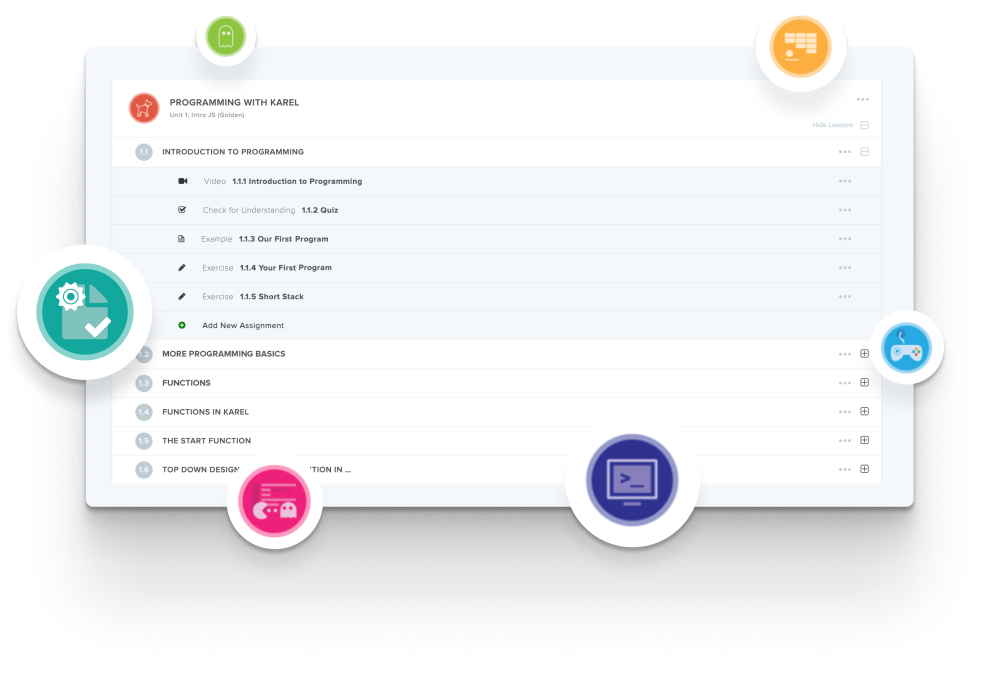
Create and organize Assignments in any CodeHS course that you're teaching. You can even add custom assignments to pre-existing CodeHS courses.
Learn MoreDidn't find what you were looking for? Here are a few links that might be useful to you.