CodeHS Cybersecurity Insider: Seasonal Activity, PD Teaching Cohorts, and More!

💘 Seasonal Activity: Spot the Romance Scam
February is the season of love, but cybercriminals know that too. Romance scams are a form of social engineering that manipulates emotions to steal money or information. These tactics show up everywhere: phishing emails, fake tech support, and job scams.
Classroom Activity: Red Flag or Real?
Present these messages to students and have them identify the warning signs:
Message 1: "I saw your profile and felt a connection. I'm working overseas on an oil rig and it gets lonely. Would love to chat! 💕"
Message 2: "I've never felt this way about someone online. My camera is broken, so we can't video chat, but I'm saving to visit you! I'm a little short on my plane ticket—could you help out?"
Message 3: "I'm a US Army captain stationed abroad. I want to send you a gift, but you'll need to pay $200 in shipping through gift cards."
Red Flags to Spot
Claims to be overseas with excuses to avoid video chat
Relationship moves unusually fast
Asks for money, gift cards, or cryptocurrency
Emergencies that create urgency
Discussion Questions
If a friend told you they were sending money to someone they'd never video-chatted with, what would you say?
How are these emotional manipulation tactics similar to phishing emails?
🗞️ Cybersecurity in the News
SoundCloud Data Breach Exposes 28 Million User Accounts
Welcome to 2026! The new year kicked off with a major data breach affecting a platform many students use daily.
In December 2025, SoundCloud confirmed a data breach that exposed the email addresses and public profile information of approximately 28 million user accounts. While passwords were reportedly not compromised, the exposed data could still be used for phishing attacks and spam.
This breach is a reminder that the apps and platforms we use every day are attractive targets for hackers. Even if passwords aren't stolen, leaked email addresses can lead to targeted phishing attempts where attackers pretend to be from trusted companies.
Read more: SoundCloud Data Breach Affects Nearly 30 Million Users
Class Discussion Questions:
If your email address was leaked in a breach, what types of phishing emails might you receive? How would you recognize them?
What steps can you take to protect yourself after learning that a service you use has been breached?
Should companies be required to notify users faster when breaches occur? Why or why not?
🚀 AP Cybersecurity Updates
The CodeHS team is expanding our cybersecurity offerings to better support teachers and students, including our new AP Cybersecurity course from College Board’s AP Career Kickstart program. CodeHS has everything you need to successfully teach this course in the fall, including professional development and a new Cyber Range.
🔥 Cybersecurity Challenge
Decode the following message using a substitution cipher:
SURWHFW BRXU SDVVZRUGV
Last Insider’s Challenge Answer
Can you decode the following message? Hint: The key to this message lies in thinking inside the square.
52 24 33 44 15 42 24 43 31 34 32 24 33
Answer: This is a Polybius Square. It uses a grid. Every pair of numbers is one letter.
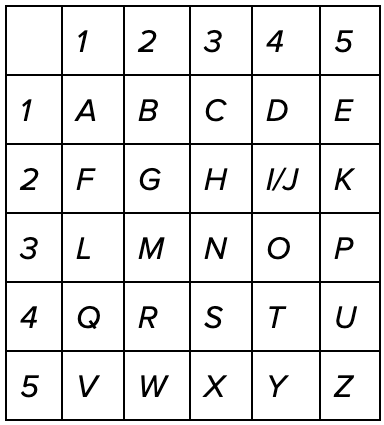
The message reads: "Winter is coming"
⚙️ PD Teaching Cohorts
CodeHS is offering year-long professional learning cohorts for the 2026–27 school year, supporting educators with guided learning, practical strategies, and a collaborative community. Educators can join cohorts focused on AP Cybersecurity, Applied AI for Educators, Teaching AP Computer Science Principles (AP CSP), or Teaching AP Computer Science A (AP CSA).
🛠️ CodeHS Product Updates Page
Check out our product changelog to stay up to date with the latest features, improvements, and fixes to CodeHS. Some exciting tools you can explore are:
💬 Stay Connected
Explore the CodeHS Cybersecurity Topic Hub
Chat with fellow teachers in the CodeHS Facebook Group
Happy Coding!
- The CodeHS Team
Interested in learning more about CodeHS Pro? Request a quote.